I’m working on a Python script which automatically generates a year’s worth of M-209 keying materials, with daily key changes. I hope that this script and its output will be useful for future M-209 activities, and add a more realistic flair to them.
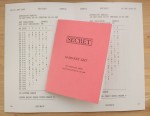
Now, the big problem is that I’ve never seen actual M-209 key lists. I’ve come up with a plain text format for individual key tables, which I think I picked up from one of the M-209 technical manuals. I know that individual keys were identified by two-letter sequences called “key list indicators”. I know that keys were intended to be changed periodically, possibly daily (or possibly more or less often depending on activity level, but I’m sticking with daily for my purposes). I’ve seen a training film in which an M-209 key list is consulted, but the video transfer of the film is too blurry to make out useful details.
From these details, I’ve inferred what I think a key list might have looked like. I’m hoping to get some input from other crypto enthusiasts about the formatting, wording, etc.
… Read More!